UK’s National Super computing Service Compromised!
On Monday 11th May at 4:30 in the evening, the UK’s national supercomputing service ARCHER notified that its security on the login nodes had been exploited. Later, ARCHER was disabled and taken offline for further investigation. Two days after the incident, the supercomputing service, working with the National Cyber Security Centre (NCSC) and Cray/HPE, reported that several other computers have also been targeted across Europe.
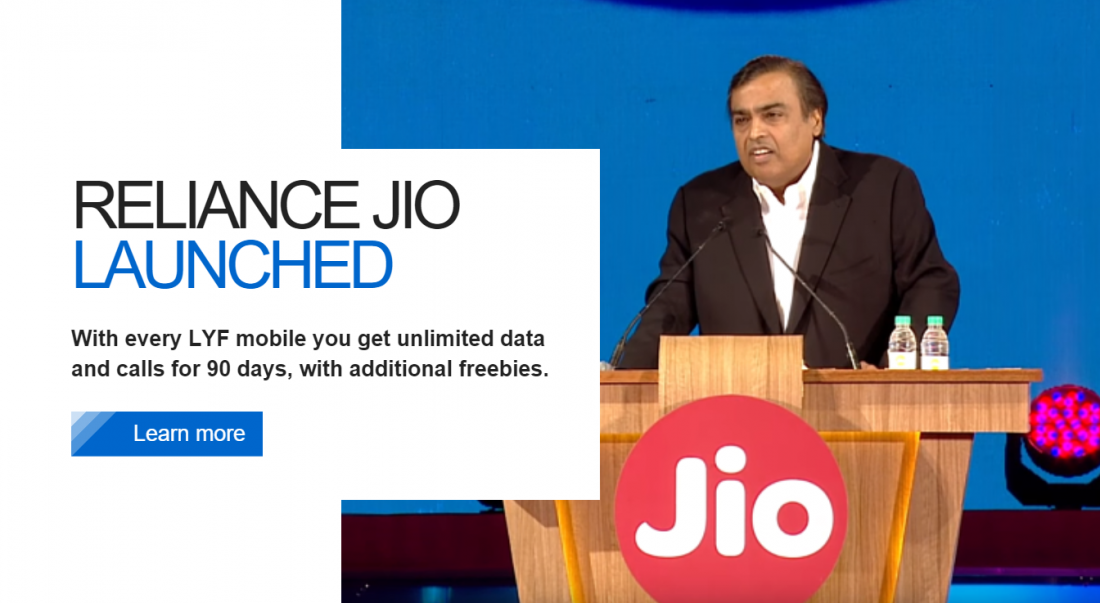
While this all was happening, the US was accusing China-backed APTs (Advanced Persistent Threats) of targeting labs, hospitals, and academic institutions working on COVID-19 related research. ARCHER was providing supercomputing services to researchers from all around the globe, involved in modeling the COVID-19 outbreak. However, at present, there is no public evidence that the intrusion was targeted in nature. In an interview with Dark Reading, Chris Morales, head of security analytics at Vectra, said regarding the cyber attack on ARCHER, “The cure for COVID might be the most valuable thing in the world right now … And, unfortunately, where there is value, there is a crime.”
ARCHER, started in November 2013, is the latest and one of the most powerful UK National Supercomputing Service. It provides supercomputing power to the users who need to run simulations and calculations that require large numbers of processing cores. ARCHER’s core hardware comprises of Cray XC30 MPP supercomputer, external login nodes, and postprocessing nodes, and the associated filesystems. It has a total of 118,080 Intel Ivy Bridge series processing cores. Each node has a total of 64 GB of memory with a subset of large memory nodes having 128 GB. However, this is currently being transitioned to a new 28 petaflops Cray supercomputer with 748,544 AMD cores.
On 15th May, it was announced that the attack has forced all existing ARCHER passwords and SSH keys for secure authentication to be changed. “When ARCHER returns to service all users will be required to use two credentials to access the service: an SSH key with a passphrase and their ARCHER password. It is imperative that you do not reuse a previously used password or SSH key with a passphrase. We are preparing new documentation which will describe the new arrangements and the Service Desk will be available to answer any concerns about this,” ARCHER said. As of now, the UK’s national supercomputing service remains offline. Unfortunately, when the services resume, the Data Transfer Nodes (DTNs), the Data Analytic Cluster (DAC), and the RDF filesystems, /epsrc and /general, will still not be available.
The FBI and the Cybersecurity and Infrastructure Security Agency (CISA) have notified that they have been investigating several cyber compromises that are targeting US organizations conducting research on COVID-19. They have said that the attackers are “non-traditional collectors” working for the People’s Republic of China.